prioritized context-aware exploit-driven remediations
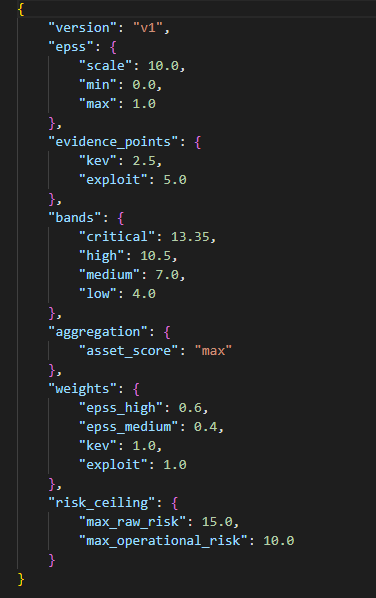
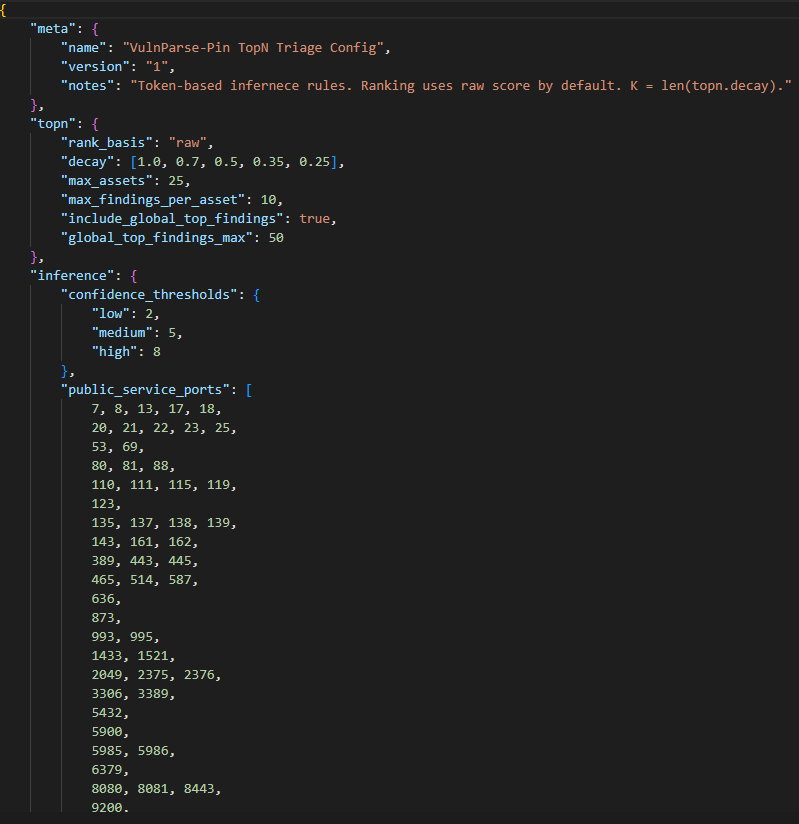
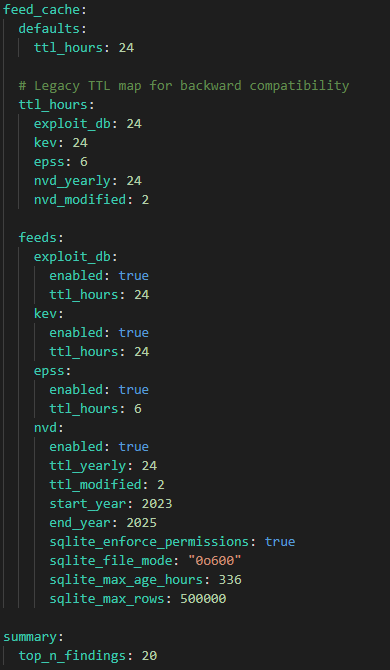
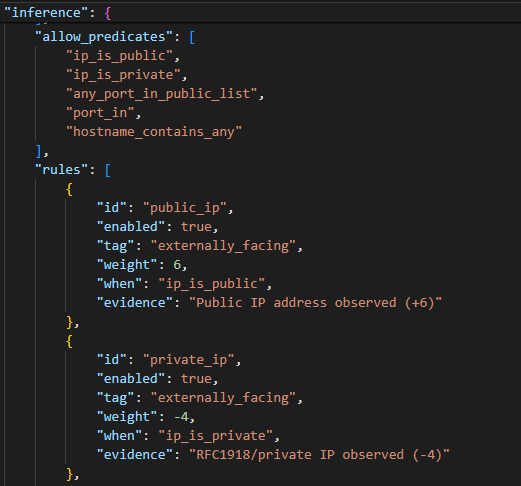
VulnParse-Pin introduces a unique idea to vulnerability management — giving users a tool that provides explainable artifacts for defensible remediation decisions, preserves input for auditability, and gives asset exposure context for realistic real-world exploitability.
All while being highly configurable to fit the needs and goals of users’ environments.

Normalize • Enrich • Score • Prioritize • Decide •
Normalize • Enrich • Score • Prioritize • Decide •
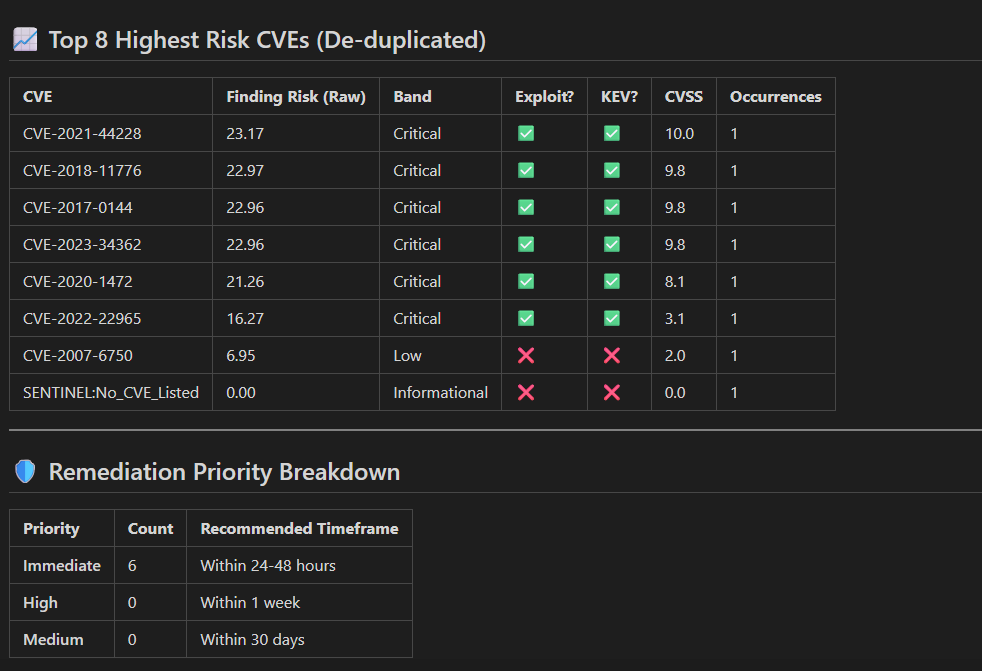
Most vulnerability data is noise
Vulnerability scanners generate thousands of findings, but they don’t tell you what actually matters.
CVSS scores severity, not risk.
Security teams ask:
Which vulnerabilities are exploitable?
Which ones to patch first?
Which ones can wait?
Outcome:
No exploit context
No environmental context
No consistency across scanner
Encumbered with manual triaging

WHAT IS
VULNPARSE-PIN
VulnParse-Pin is what analysts and engineers wish vulnerability management tools really did: Reduce vulnerability noise and raise the vulnerabilities that present real-world exploitable risk given the context of their environment.
Does a realistic attack path exist?
Is this asset externally facing and exploitable?
Does an exploit exist but it’s behind an isolated VLAN?
These are the types of questions VulnParse-Pin exists to answer in determining whether a vulnerability gets immediate attention, or sits lower in the queue for remediation.

check out vulnparse-pin on github
Contact Us
Want to collaborate? Want more information? Just share a few details, and we'll be in touch soon. We're excited to connect with you!
If you have questions or would like to submit feedback, click the button below to send an email!